Zcash Privacy: Why Your Transactions Are Not Invisible
Real-world limitations of Zcash privacy.

In a crypto market that many believed had grown saturated, one beacon of revival stands out: Zcash (ZEC). By late 2025, ZEC had surged over 400–500 % year-to-date, climbing from well under $100 to above $500 by December. Its market-capitalization crossed the $10 billion mark and, for the first time, overtook longtime privacy-leader — Monero.
Privacy is back. Hackers, fraud rings, and on-chain analysts can now trace almost any transaction made by everyday users or businesses. This level of visibility exposes wallets, financial flows, and even physical identities — putting funds and, in extreme cases, personal safety at risk.
Users have increasingly turned their attention to Zcash as a privacy-focused cryptocurrency. But here’s the catch: despite its cutting-edge zero-knowledge-proof technology (zk-SNARKs), Zcash’s real-world privacy falls far short of what it promises.
In this article we’ll dive into how Zcash’s privacy architecture really works, where it fails, and what that means for users that believed they were invisible.
Key Takeways
- In Zcash, privacy is optional, not the default. Most transactions still go through fully transparent addresses — just like Bitcoin.
- True privacy only happens when funds move strictly between z-addresses. In reality, those transfers are pretty rare.
- Less than a quarter of all ZEC is actually shielded. Because the private pool is so small, shielded transactions stand out and are easier to trace.
- UPD 12/09/2025: Arkham de-anonymized more than 53% of all Zcash transactions. One of the largest holders of the cryptocurrency turned out to be the U.S. government.
- Even if z→z transfers are always used, repeated addresses, identical amounts, send times, and filled memo tags give the user away.
- Exchanges often only work with transparent addresses, and crypto wallets do not hide IP addresses.
- Zcash is inconvenient and volatile for businesses, which is why external solutions (such as BitHide) are needed to ensure data protection on any network.
How Zcash Privacy Works and Where It Breaks in Real Life
Zcash was created as a privacy-first fork of Bitcoin, powered by zk-SNARKs, a form of zero-knowledge proofs capable of hiding the sender, receiver, and transaction amount. On paper, it is one of the most advanced cryptographic privacy systems in any public blockchain.
In practice, however, Zcash’s privacy depends far less on cryptography and far more on how users, wallets, and exchanges actually handle ZEC.
Two Address Types: Transparent vs. Shielded
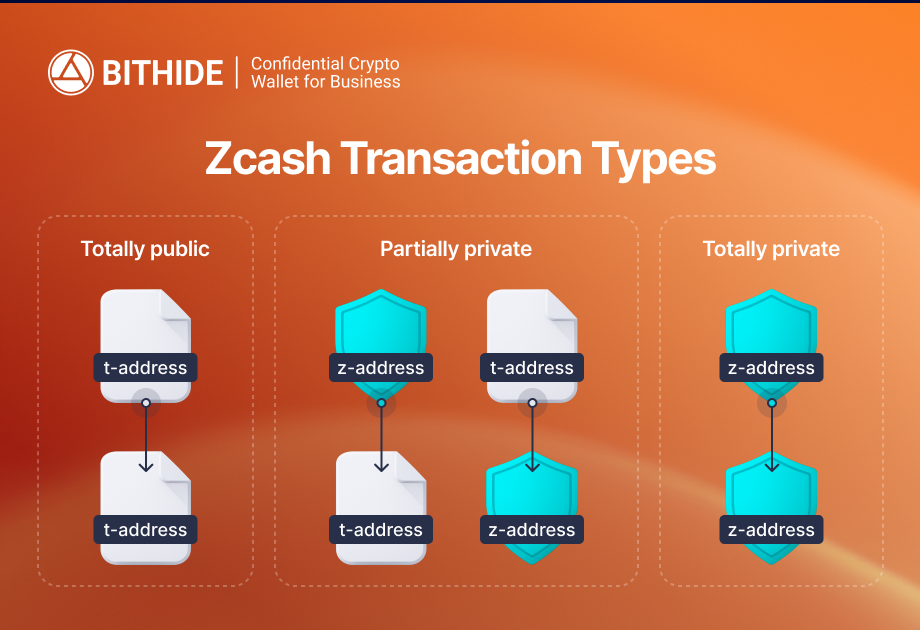
Zcash operates with two fundamentally different address formats:
- t-addresses (transparent) — fully public, identical to Bitcoin’s transparency model.
- z-addresses (shielded) — private, where zk-SNARKs conceal all transaction details.
True confidentiality is only achieved in z → z transactions. Yet the ecosystem defaults heavily toward transparency:
- Most centralized exchanges only support t-address deposits and withdrawals.
- Many mobile wallets use transparent addresses by default.
- Mixed flows like t → z → t still leak patterns, amounts, and timing metadata.
As a result, even though Zcash offers strong cryptography, the majority of ZEC activity never becomes private at all.
Technical Limitations of Zcash Privacy
The privacy model around ZEC has several structural limitations that affect how protected users actually are — even when transactions are shielded.
Privacy in Zcash Is Optional, Not Guaranteed
Unlike Monero, where every transaction is private by design, Zcash leaves privacy as a choice. Users can transact through either transparent (t) or shielded (z) addresses, and most wallets, exchanges, and mobile apps default to the transparent option.
A Small Shielded Pool Reduces Anonymity
By the end of 2025, the shielded pool still accounts for a minority of ZEC activity — roughly 20–25 % of the total supply. This doesn’t break the cryptography, but it weakens the anonymity it provides. When only a small percentage of users transact privately, shielded operations stand out. Analysts can more easily correlate the few shielded transactions with their transparent entry and exit points, or spot rare patterns that would disappear in a larger pool.
Patterns Matter More Than zk-SNARKs
Even completely shielded transactions can be deanonymized when external patterns leaks. Wallet reuse, regular timing patterns, predictable transaction amounts, memo fields, and user actions around the shielded pool often reveal more than the protocol hides.
In other words, privacy in Zcash depends heavily on operational behavior — and most users don’t maintain the discipline required to stay anonymous.
The Ecosystem Around Zcash Is Not Built for Privacy
While the protocol supports private transfers, the surrounding ecosystem works against it. Most exchanges require t-addresses, and some wallets log metadata or expose timing information. These factors create a trail that can be linked together even without decrypting any shielded data.
Network-Layer Exposure Remains a Critical Weak Point
Zcash does not hide IP addresses. When a wallet broadcasts a shielded transaction, the sender’s IP address is exposed to the network. It goes to a node, and many nodes are controlled by hackers or fraudsters. A VPN won’t help — user data often leaks into the network through hacks or is sold by dishonest employees.
This has been one of the most common real-world deanonymization methods: investigators follow the network footprint, not the zero-knowledge proofs.
UPD 12/09/2025: Arkham Deanonymized Over 53% of All Zcash Transactions
The analytics platform Arkham has deanonymized more than 53% of all Zcash transactions, totaling $420 billion, including both public and private ones. Over 48% of inputs and outputs have been linked to identifiable entities, including well-known individuals and organizations.
One of the largest holders of Zcash turned out to be the US government — in 2018, authorities seized ZEC worth approximately $737,000 from AlphaBay darknet market founder Alexandre Cazes. Over the years, the value of these assets has roughly doubled.
Zcash creator Zooko Wilcox partially disputed Arkham analysts' claims. According to the developer, the platform has not deanonymized “a single ZEC” stored in shielded pools, as this is simply impossible.
Common Mistakes in Using Zcash
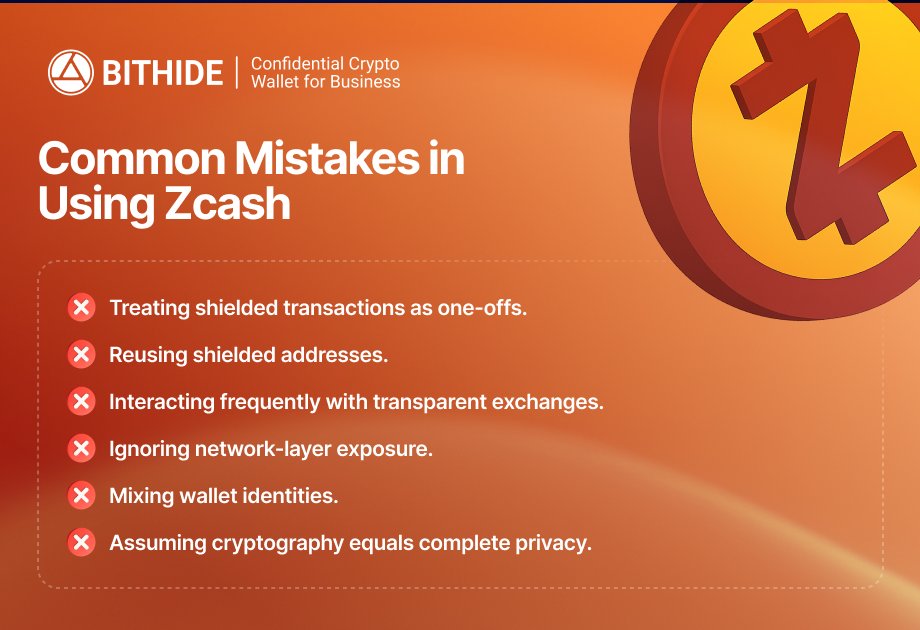
Most users don’t try to understand how Zcash actually works. They simply trust its basic anonymity and make typical cryptocurrency usage mistakes that nullify its strong cryptography.
Treating Shielded Transactions as One-Offs
Many users assume a single z → z transaction automatically anonymizes all their activity. In reality, if preceding or subsequent transfers occur through transparent t-addresses, patterns remain easily traceable.
Reusing Shielded Addresses
Repeatedly using the same z-address or sending predictable amounts creates identifiable patterns. This weakens the privacy zk-SNARKs provide and makes deanonymization easier for hackers and analysts.
Interacting Frequently with Transparent Exchanges
Every time ZEC touches a t-address on a KYC exchange, metadata like deposit time, withdrawal size, IP address, and device info can be logged, collapsing the anonymity set for shielded transactions.
Ignoring Network-Layer Exposure
Zcash does not hide IP addresses. Users relying only on VPNs or standard connections risk exposing their location and identity, as network activity can be logged, sold, or correlated with other blockchain actions.
Mixing Wallet Identities
Linking multiple wallets to the same device, browser, or exchange account reduces privacy. Even shielded transactions can become linkable if operational identities overlap across wallets and services.
Assuming Cryptography Equals Complete Privacy
Strong zk-SNARK cryptography protects transaction details but cannot mask user behavior. Poor operational habits, predictable transaction patterns, or small shielded pools make deanonymization possible.
Protecting Business Confidentiality Beyond ZEC
While Zcash offers powerful cryptography, its volatility and low adoption (compared to BTC, ETH, or stablecoins) make it impractical for routine business operations. Therefore, companies must protect sensitive data in transactions involving currencies that lack Zcash's strong native privacy.
A Solution for Secure Cryptocurrency Operations — BitHide
BitHide is a non-custodial crypto wallet for companies. Its architecture includes solutions to protect business data from criminals, hackers, and competitors:
- Temporary addresses for blockchain fee payments. Prevent transaction clustering. Users set a threshold after which the address stops working and is replaced with a new one.
- Non-custodial architecture. The company does not rely on third parties and independently manages the seed phrase, private keys, and controls servers running the wallet software.
- Real-time backups. Wallet usage history is constantly saved in the cloud in encrypted form. One of our clients was able to restore operations almost instantly after equipment was seized from their office during an armed attack.
- Data encryption. In addition to encrypting transaction history, clients can set up callback hashing to protect against interception or compromise.
- Role-based access. Depending on their responsibilities, company employees receive different levels of access. This significantly reduces the effectiveness of social engineering and lowers the risk of internal abuse.
Conclusion
Despite its zk-SNARK technology, Zcash’s privacy is limited by ecosystem practices and user behavior. Most transactions default to transparency, making wallets and financial flows traceable. To protect assets and sensitive operations from malicious actors, consistent shielded transactions, address rotation, network-layer obfuscation, and operational separation are required.
For businesses, Zcash is highly inconvenient, and it is necessary to use payment solutions that protect confidentiality even when a company uses cryptocurrencies that do not offer default privacy protection. Contact the BitHide team to learn how this crypto wallet can safeguard your financial flows.


